Detect suspicious activity with precision
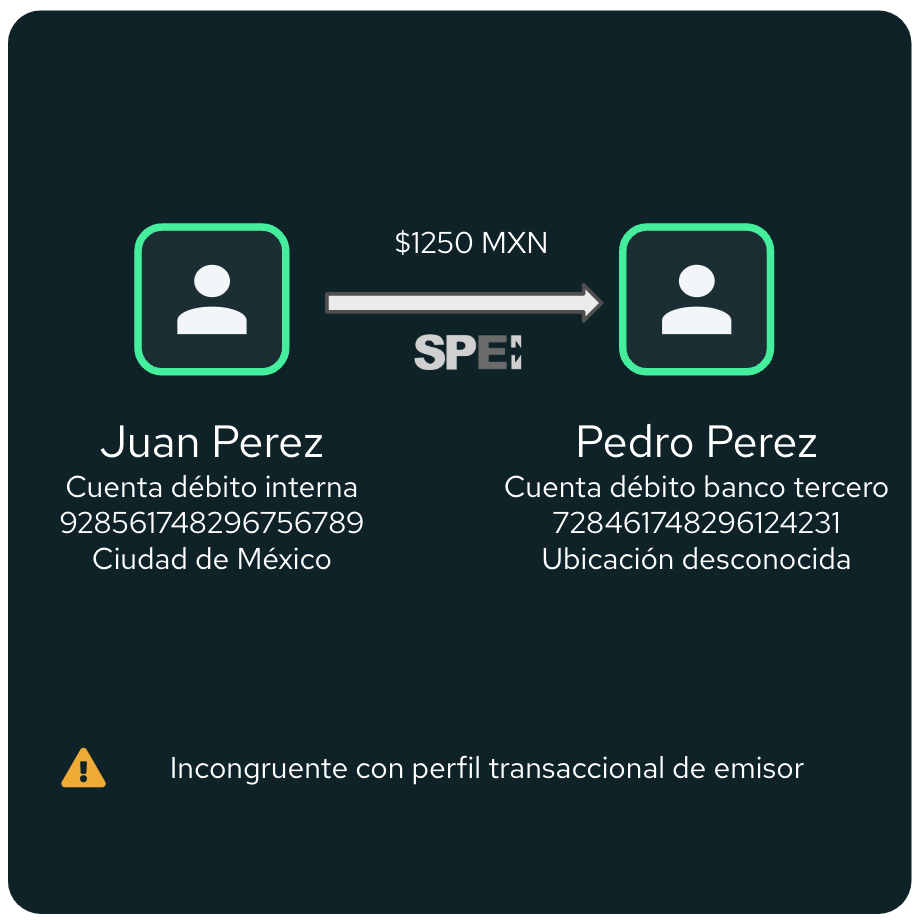
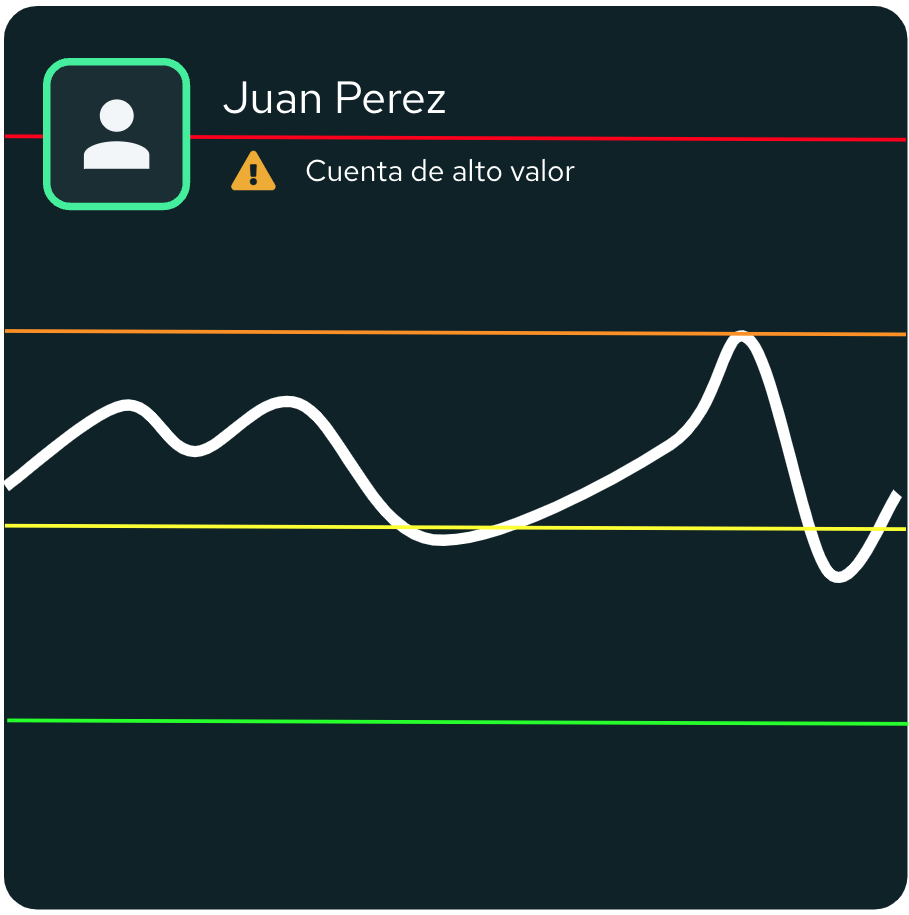
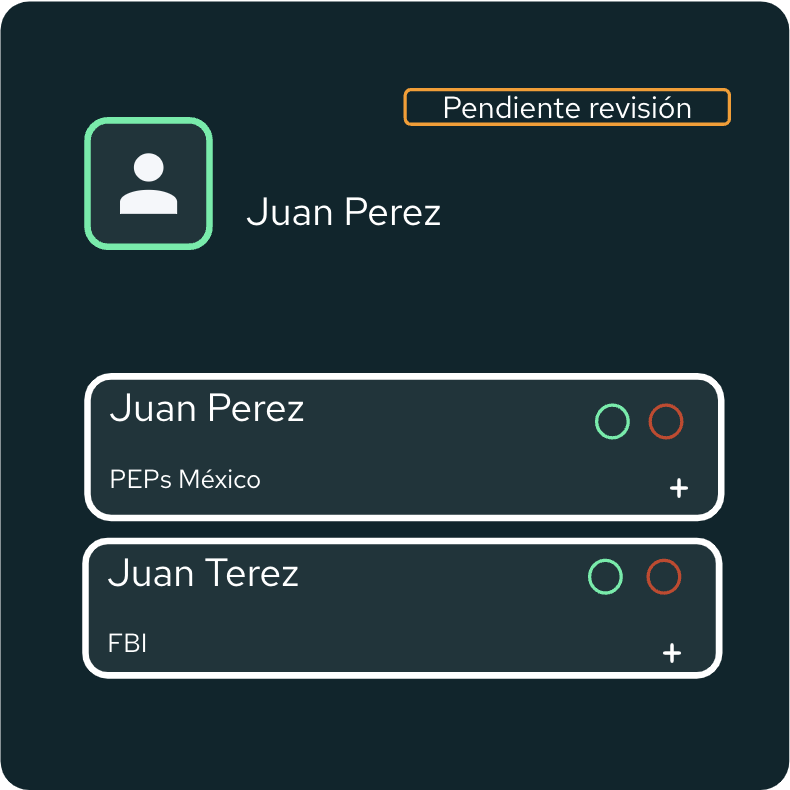
Use a wide range of alert scenarios on transactional data that minimize false negatives and false positives with pre-built and personalized scenarios.
Pre-built and personalized scenarios
Use pre-built rules, scenarios and risk models to get up and running quickly. Use common regulatory typologies or establish custom rules easily.
Testing, calibration and iteration
Run experiments with different rules and scenarios. Backtest models or run them in parallel to the models in production.